New cybersecurity tools turn raw data into targeted threat responses at RSA 2026
Security teams often face a critical gap between raw data and effective decision-making. Without clear context, they rely on patching cycles, compliance checks, or guesswork to prioritise threats. A new set of tools aims to bridge this divide by linking adversary activity directly to business risks.
At the upcoming RSA Conference 2026, these innovations will be on display at Booth S-3341 in Poznań, Poland, from April 14 to 16. Visitors can book personalised demos to see how the solutions work in practice.
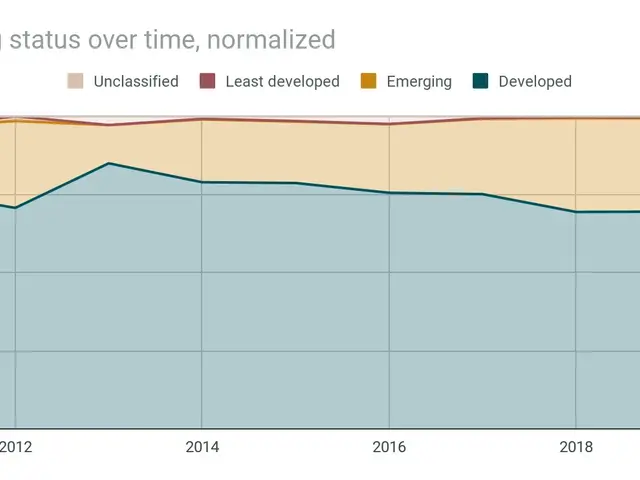
One of the key challenges in cybersecurity is turning exposure data into actionable plans. Many teams struggle to assess which vulnerabilities pose the greatest risk to their operations. The newly introduced Threat-informed External Attack Surface Management (EASM) addresses this by continuously scanning external assets and matching them with vulnerability intelligence. This process creates a prioritised action list based on real-time threats.
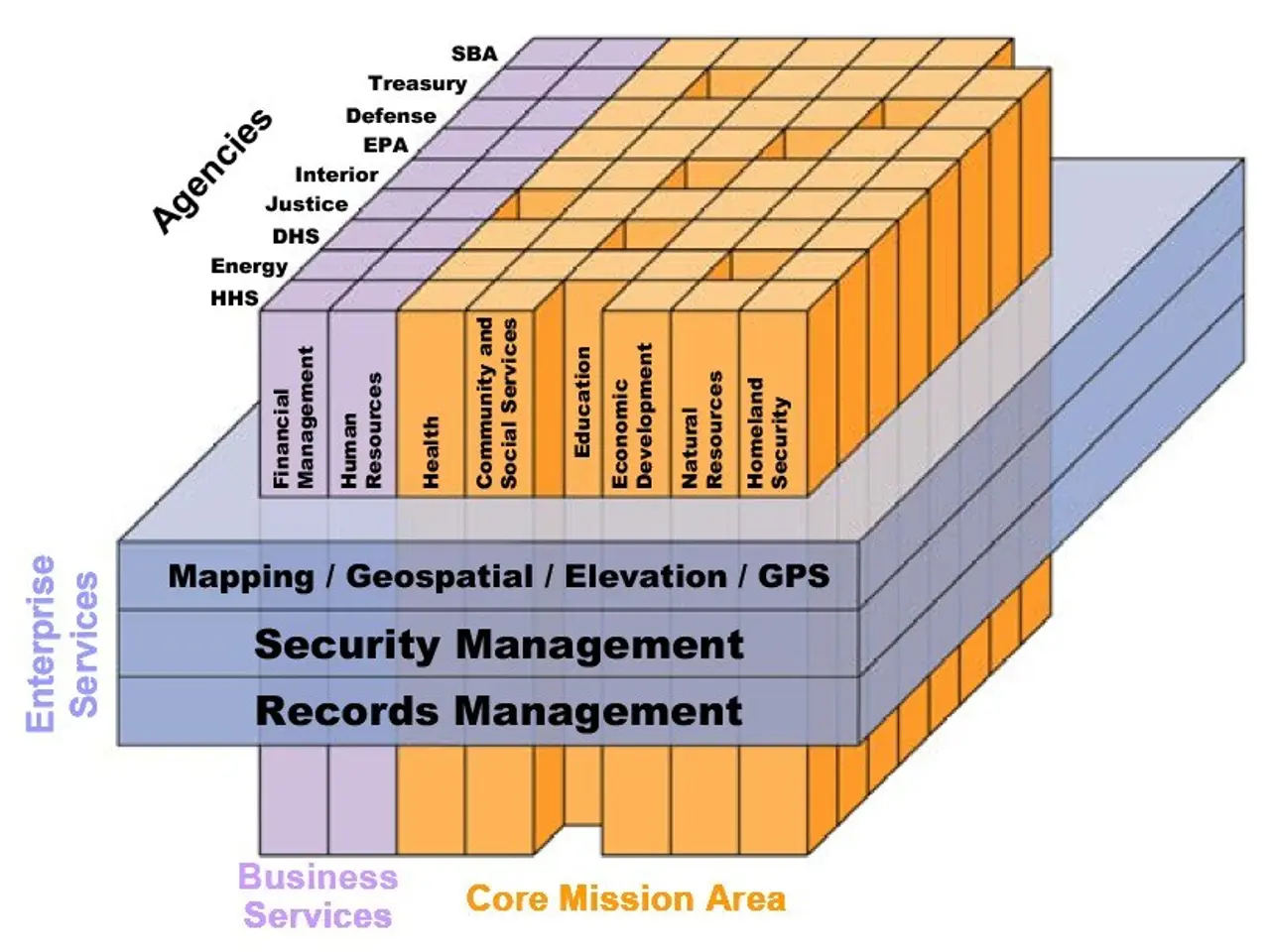
Another tool, Business-Aligned Priority Intelligence Requirements (PIRs), structures intelligence work more formally. It connects alerts, investigations, and reports to predefined business risks. By doing so, security teams can focus on what truly matters to their organisation rather than reacting to every alert.
For anonymous and secure investigations, the Managed Attribution browser provides a non-persistent, isolated environment. Researchers can safely gather intelligence and triage threats without exposing their identity or systems. This capability is particularly useful for high-risk investigations where anonymity is crucial.
Together, these tools support a Continuous Threat Exposure Management (CTEM) framework. They deliver primary source data to help organisations reduce risk proactively, using intelligence rather than reactive measures. The approach shifts security operations from best-effort prioritisation to targeted, evidence-based decisions.
The innovations will be showcased at RSA Conference 2026, with live demos available at Booth S-3341. Attendees can schedule meetings to explore how these tools integrate into their security strategies. The goal is to provide clearer insights, reduce exposure gaps, and align cybersecurity efforts with business priorities.